Cyber House Rules
Password Day
Meet Alice and Bob!

They live in this house, the Cyber House:

They are super, but their power isn’t from some radioactive spider or what not, it’s cybersecurity.
They work for the Global Dessert Vault, the international authority responsible for maintaining all of the recipes for the world’s best desserts.
You’ve been recruited to train with them and learn how to protect our world from their arch nemesis known only as the l33k3rs.
As you all enter the Cyber House they show you what they’ve found: a secret dialogue between two l33k3r agents
They found this package and are convinced there is more than meets the eye:

Apparently there is a briefcase hidden in there somehow.
Your Training Begins
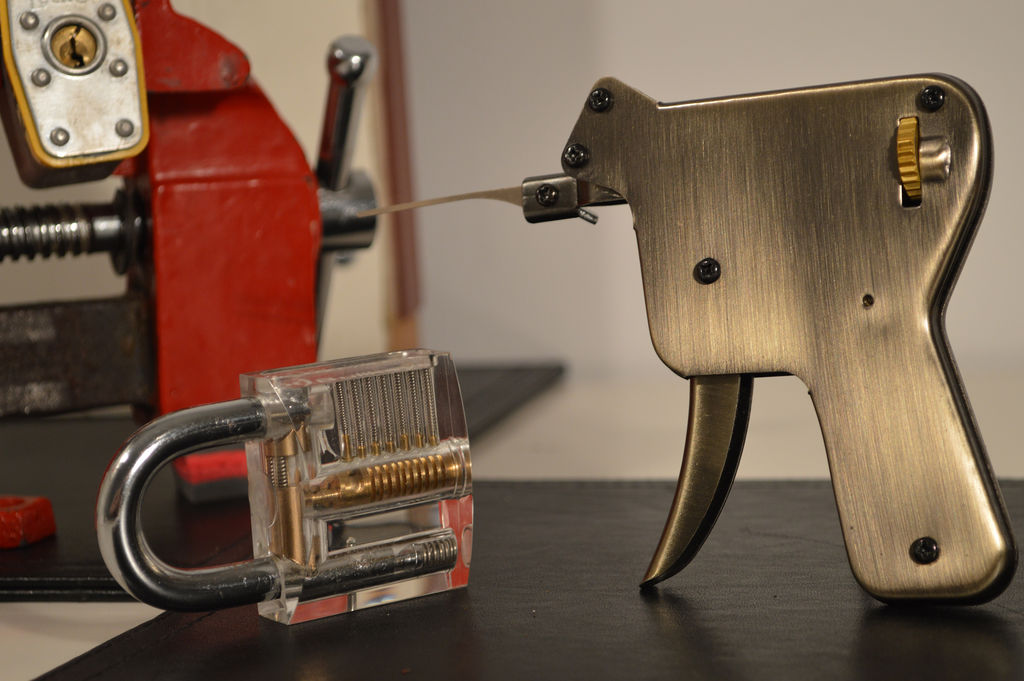
Alice and Bob believe in you, and our desserts are counting on you. The first lesson they want to teach you is how to evaluate the security of a locking mechanism. If you’re protecting important recipes you’ll need a secure lock, but you can’t just take someone’s word for it. They hand you a credit card, a lock-picking kit, a hammer, and some sort of auto-lock pick.
You’re going to learn just how secure doors really are (or aren’t)!
To practice exercises, go to learnification.fun!
Go to Modules and select, ‘Week of Cyber Day 1!’
Each time you crack a lock, copy the flag and insert it into the answer box. Then the next lock will appear!
- Exercise 1: For the first lock it looks like a job for your credit-card:

- Exercise 2: Here you will break another password however this one is hash protected.

- Exercise 3: Another password hack! When you have a hammer everything is a nail…

- Exercise 4: Last password hack. Let’s use the power of automation!
Today’s Big Mission
Open the briefcase, find the secret message!
You’re ready to crack the l33k3rs secret code. Let’s find their briefcase and use our new skills to find the secrets to their nefarious plot.

We will now attempt to uncover zipfiles hidden within an image. We will do this using the terminal.
- The terminal is a way to speak with your computer more directly without using your mouse.
We are going to try and uncover the secret message within the package that was intercepted from the l33k3rs!
To start this exercise, go to this page!
Once you’ve found the secret message, put it into learnification.fun! to claim today’s certificate!
Maybe we can show you how to send your own secret messages in images…
The Call
We need you
Alice and Bob believe you’ve got what it takes. In so they are presenting you with a badge for your achivements today. They want you to join them in the fight to protect the world’s dessert recipes (and power grid, the internet, our banks, Netflix, and all of the other things needing protecting).
Let’s look at the jobs you could do!
Put this badge on your website, this is the link to the image: https://udel.codes/cyber1/Password_Cracker.png
